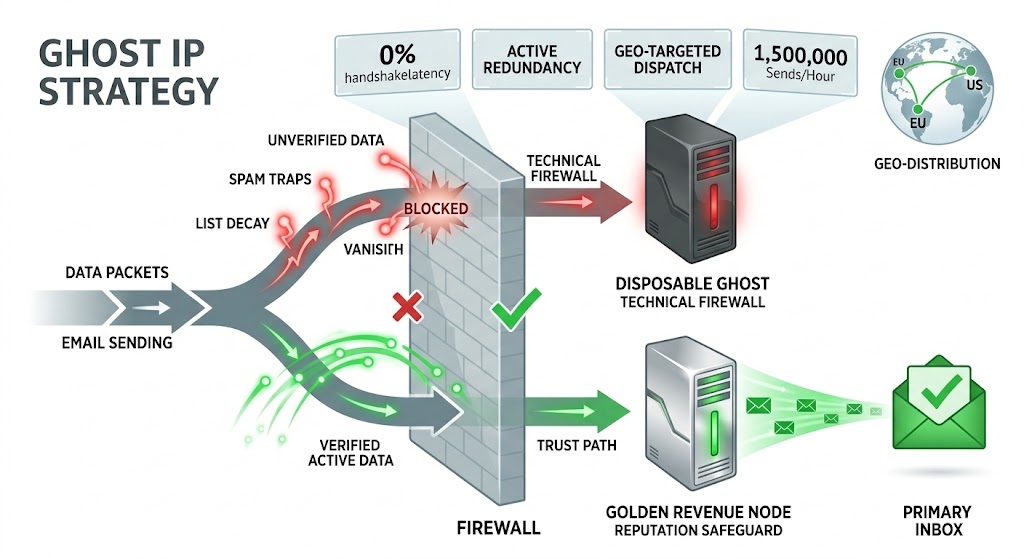
Protect your reputation with the Ghost IP strategy to ensure your primary sending domain remains entirely clean while you test and scale new data. To succeed in 2026, senders must abandon the practice of using a single “Golden” infrastructure node for both nurturing and cold acquisition. Instead, a multi-tiered system, built on the total isolation of high-risk operational activity, is non-negotiable. This diagnostic model allows you to sacrifice disposable scouting nodes to “hunt” for spam traps and list decay, preventing these threats from ever touching your core assets.
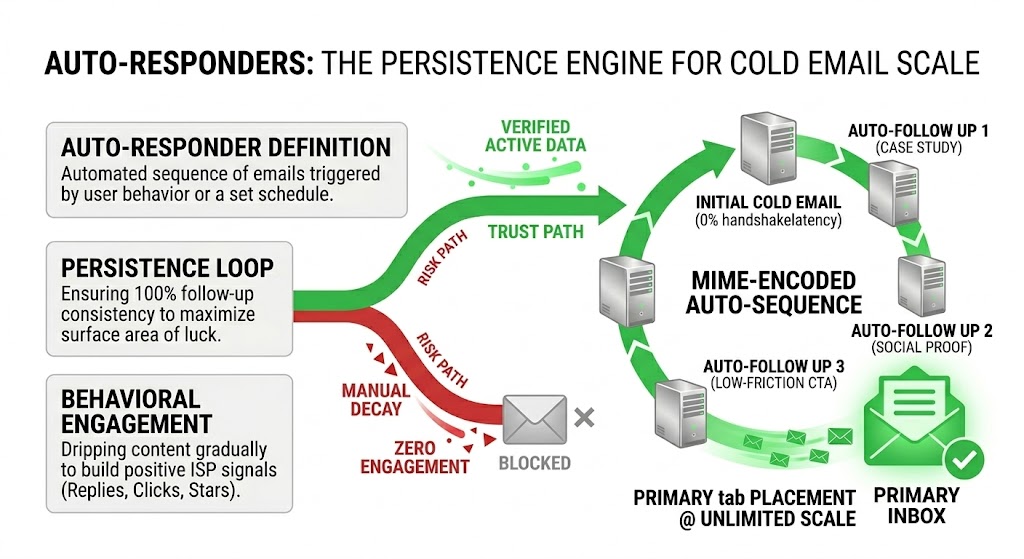
The landscape of 2026 has introduced new pressures for enterprise senders. ISPs like Gmail and Yahoo now utilize sophisticated, machine-learning-based Behavioral Filters that analyze engagement at the technical handshake level. A single “Pristine Spam Trap” hit—a mailbox specifically created to catch bulk senders—can generate a catastrophic negative signal, triggering automatic volume throttling, domain down-ranking, or total blacklisting.
Relying on list cleaning services is an 80% solution; they catch obvious bounces and typos, but they often fail to identify active trap networks or aged, recycled accounts that anti-spam entities monitor. A true deliverability architect must assume that raw data is “poisoned” until technically proven otherwise. This requires a shift from a defensive posture to an offensive, infrastructure-driven strategy. By implementing the Ghost IP model, organizations turn their infrastructure into a layered defense system, ensuring that only verified, high-engagement data reaches the core “Golden” domain.
1. Multi-Tiered Infrastructure Design: Decoupling Risk
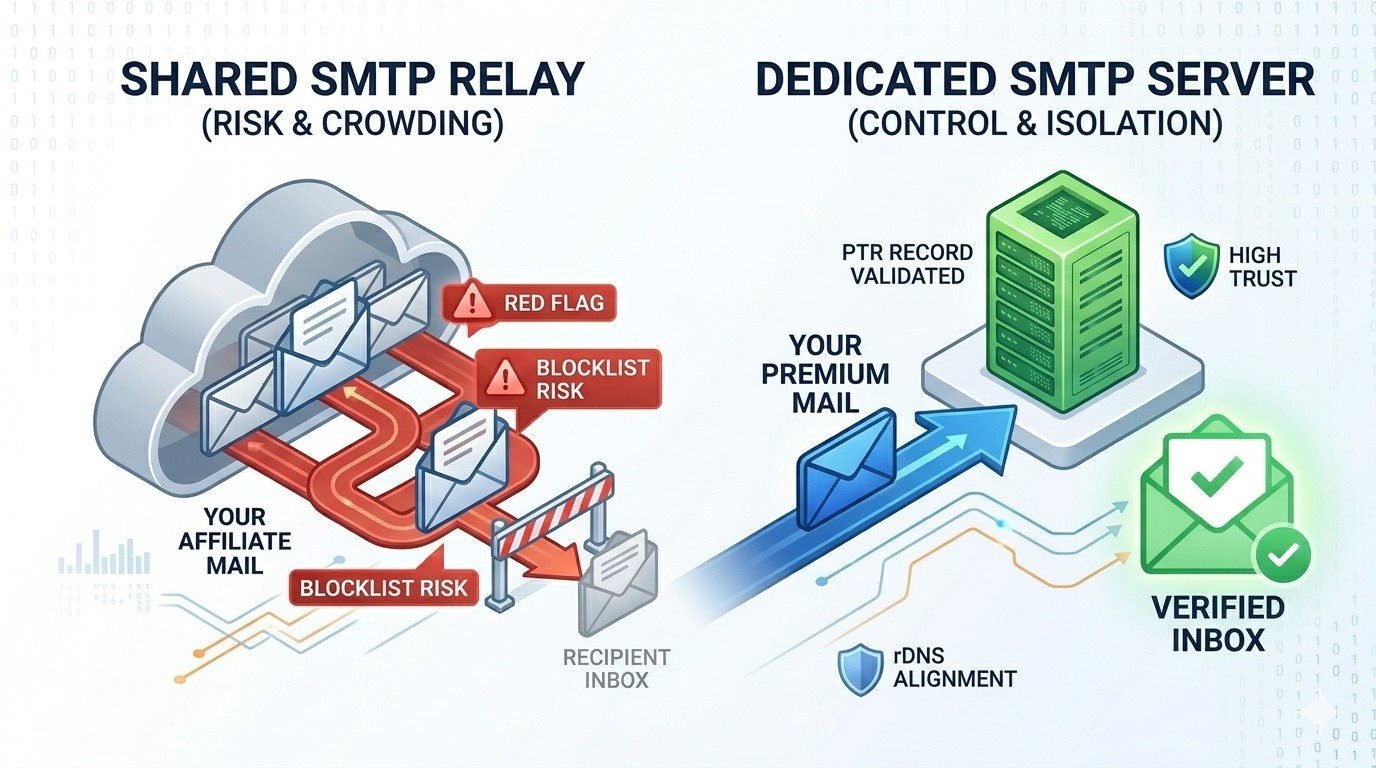
The foundational principle when you protect your reputation with the Ghost IP strategy is decoupling high-risk operational activity from your core transactional assets. Traditional systems fail because they treat all data and all sends equally, operating everything on a single, warmed server cluster. This monolithic design is fundamentally flawed; if one cold campaign hits a toxic list segment, the resulting blacklist event will affect critical customer nurturing and transactional emails.
A. Total Isolation through Node Tiering
A resilient infrastructure requires a clear separation of concerns based on data maturity. You must manage your assets in two distinct server clusters.
-
The Golden Revenue Node: This warmed infrastructure handles your high-intent, active audience only (previous openers, clickers, and verified leads). It never, under any circumstances, sends mail to raw, unverified data. This node protects your primary domain reputation.
-
The Ghost Scouting Node (The Sentinel): This is a disposable, short-lived server instance. It is not designed to build long-term trust. Senders specifically utilize it to “scout” unverified data for technical and behavioral traps. If the reputation of a Ghost Node dies, it is architecturally irrelevant. You simple burn the IP and spin up a new instance. This node exists only to provide the diagnostic intelligence necessary to protect your reputation with the Ghost IP strategy.
B. Anti-Footprinting Measures
A critical component of the strategy is ensuring anti-spam systems cannot link your Ghost network to your Golden domain through recursive footprinting. Your tiers must not share technical signatures. You should deploy Ghost Nodes across different data center ASNs (Autonomous System Names), ensuring diverse IP subnets and PTR/rDNS patterns. Maintaining complete architectural asymmetry ensures that a negative signal generated on a scouting node remains localized and does not affect your core assets.
2. Handshake Analysis: Using Ghost Nodes to Hunt Spam Traps
When you protect your reputation with the Ghost IP strategy, you convert high-volume sending into a diagnostic process. Standard list validation services can only look at the data statistically, but by sending mail through a Ghost Node, you look at the list behaviorally. This “Sacrificial Send” uses technical handshakes to identify list decay and threats before your primary infrastructure ever interacts with the data.
A. SMTP Response Signals as Diagnostics
ISP filters respond differently based on the type of threat they detect. Senders must analyze SMTP response codes to differentiate between simple list decay and toxic reputation traps.
-
Hard Bounce (550 – Account Disabled): The account is closed, but the signal indicates aged data. While this decays reputation, it is less lethal than a trap hit.
-
Throttling (421 – Connection Throttled/Too Many Connections): This signal often occurs when your scouting node sends too fast for a low-reputation IP. It is an operational bottleneck, not necessarily a toxic list signal.
-
Silenced Send (The Stealth Signal): This is the signature of a toxic threat. If your Ghost Node sends 10,000 emails and sees 0 bounces or rejections, yet receives 0 engagement, it has likely hit a trap. ISPs and anti-spam networks rarely send rejection codes for pristine trap mail; they silently record the IP, analyze the hash of the content, and update the global blacklist. Identifying these silent anomalies on a Ghost Node is how you protect your reputation with the Ghost IP strategy.
B. Tiered Data Migration
Only after a list segment has cleared the Ghost “firewall” with a 0% toxic signal should it be prioritized and migrated to your Golden node. The strategy is straightforward: use Ghost nodes to identify the 10,000 “safe” and active leads from a raw pool of 100,000, and only then feed those verified contacts into your main revenue engine.
3. Mastering Volume “Jitter” to Bypass Behavioral AI
In 2026, Behavioral AI models analyze the pacing, consistency, and sequence of SMTP handshakes to detect automated sending platforms. Bulk servers naturally send in perfectly timed intervals (e.g., exactly 1 email every 1.5 seconds) and in predictable alphabetical domain sequences. These “patterns of scale” are major footprints that lead to automatic filtering.
Randomization as a Deliverability Tactic
When using infrastructure designed to protect your reputation with the Ghost IP strategy, randomized sending behavior—often referred to as Infrastructure Jitter—is mandatory. You must technically configure your MTAs (Mail Transfer Agents) to mimic a decentralized human workflow:
-
Randomized Pauses (Jitter Pauses): Instruct the MTA to randomize the pause between individual emails (e.g., varied between 0.8s and 4.5s) to erase predictable volume spikes.
-
Varied Connection Lengths: Randomize how many emails the server sends per connection before closing and reopening a new session with the receiving ISP.
-
Non-Linear Queue Dispatch: Ensure your queue processor does not send mail in a linear domain sequence (e.g., all Gmail, then all Outlook). By randomizing the domain mix, you avoid triggering local rate-limits and shadow-bans that often result from linear domain-level blasts.
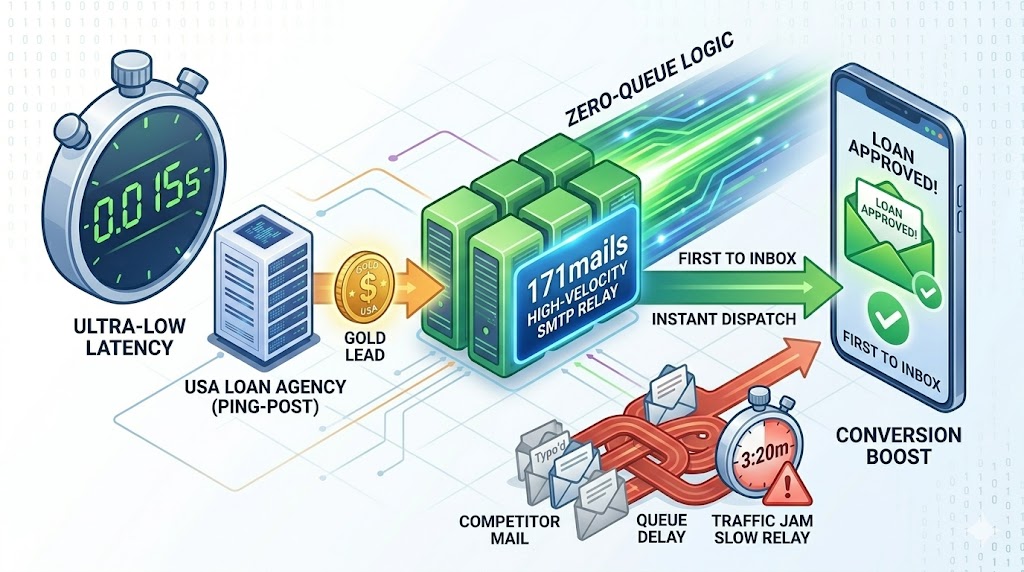
4. IP Warming Redundancy: Ensuring Long-Term Stability
One of the major weaknesses in modern email infrastructure is the “warming bottleneck.” Traditional senders stop acquisition while warming new IPs, sacrificing revenue for deliverability. A robust architecture designed to protect your reputation with the Ghost IP strategy solves this by treating warming as an active, continuous, and automated background process.
The Automated Warming Rotation
The goal is to maintain redundant, pre-warmed IPs that can be activated instantly as Golden Nodes when needed. This requires an MTA configured with automated warming schedules (IP rotation). You configure the MTA to “trickle” a micro-volume of high-engagement mail (such as password resets or transaction confirmations) through new IPs over 4–6 weeks. This automated background warming builds high-trust reputations and creates redundant capacity. When a current IP subnet eventually decays or needs rotation, you can seamlessly activate your pre-warmed nodes. This continuous technical preparation is how you effectively protect your reputation with the Ghost IP strategy.
Quick Summary
To protect your reputation with the Ghost IP strategy, email senders should configure their systems to isolate high-risk operational sends from their primary sending domain. This architecture uses disposable "Ghost IPs" to test unverified lists for spam traps and list decay before migrating verified contacts to the primary "Golden" domain. This isolation prevents anti-spam networks from footprinting core infrastructure and ensures long-term domain health in 2026.